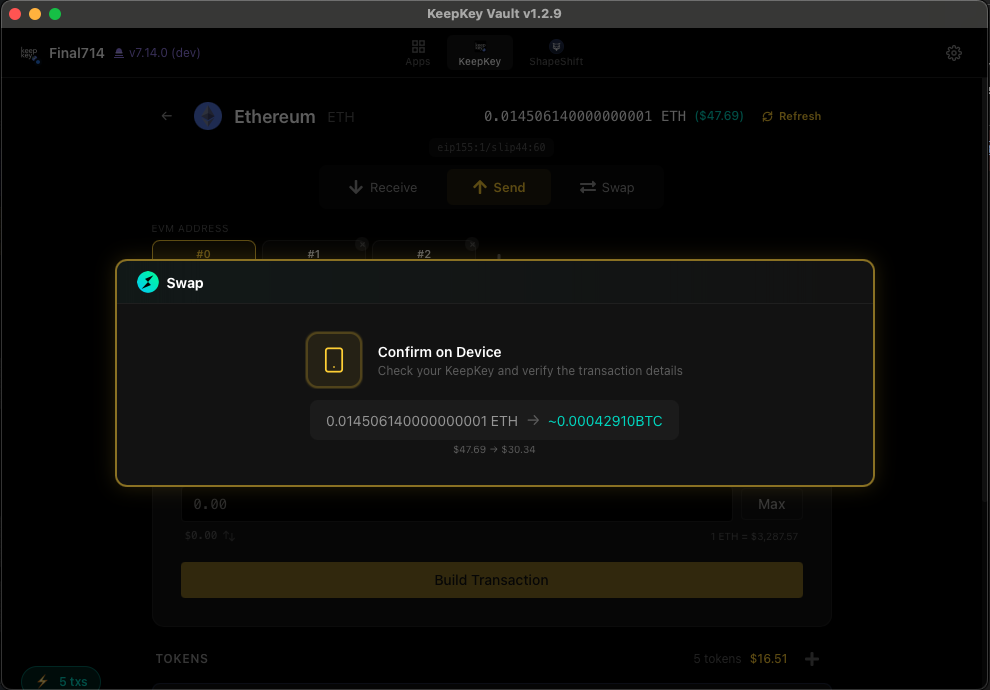
Verifying Transactions
Always confirm the address and amount on your KeepKey before approving. Your computer can be compromised — your device screen cannot. This matters most for large transactions, but the habit is worth building from day one.
Why the device screen is the source of truth
The KeepKey has its own small screen, its own buttons, and its own tiny computer that runs nothing except the signing firmware. That firmware is audited and cryptographically signed. It cannot be modified without you explicitly approving a firmware update — and even then, only KeepKey-signed firmware will install.
Your computer, by contrast, runs web browsers, dozens of apps, and potentially malware you don’t know about. A sophisticated attacker could:
- Modify what you see in the desktop application (show you the “right” address while actually signing a different one)
- Inject a different recipient address at the last moment
- Change the amount you think you’re sending
None of that affects what the device itself displays. The device shows you the real address, the real amount, and the real transaction data. It’s the last honest thing between you and your funds.
What to check on the device
Every time you approve a transaction, pause and read the device screen:
For sends and swaps
- The recipient address — every character. Compare the address on the device to the address you expected to send to (not the one on your computer). Check the entire string, character by character. Do not just glance at the first and last few characters: GPU-accelerated “vanity” grinders like Profanity can produce look-alike addresses that match a given prefix and suffix in minutes. This is exactly how the 2022 Wintermute drain (~$160M) worked — attacker-generated addresses matched the real ones at both ends, and partial checks missed the middle.
- The amount. Does it match what you intended to send? Watch the decimal places — it’s easy to send 10× what you meant.
- The asset and network. Is this the token you expect, on the network you expect? Sending ETH on Polygon is not the same as sending ETH on mainnet.
For token approvals (EVM)
- The token contract. Is it the token you actually use?
- The spender address. Is this a contract you trust?
- The allowance. Is it “unlimited” (high risk) or a specific amount (safer)?
For EIP-712 typed data
- The domain. Is this coming from the dapp you think it’s coming from? A malicious site can craft messages that look like they’re from Uniswap but actually authorize something else.
- The fields. Read what you’re actually signing. If it doesn’t make sense, cancel.
The golden rule
If you can’t explain what you’re signing in your own words based on what the device shows, don’t approve it. Cancel, figure out what’s going on, and try again once you understand.
Related
- Send & Receive — how send/receive flows work
- Swap — cross-chain swap flow